Outsourced IT Services
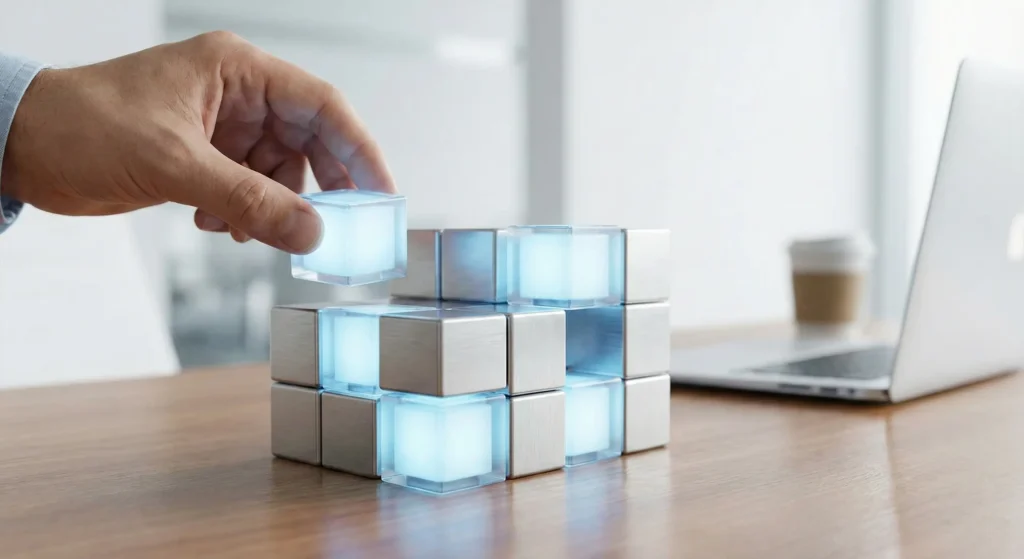
Leave your IT operations to us and focus on your business.
Outsourced IT services enable organisations to manage their IT processes through an expert team.
This model; while controlling costs, continuity, expertise and operational efficiency it's a win-win.
We don't just take over your IT processes; improve, standardise and make it sustainable.
Who are Outsourced IT Services Suitable for?
- Organisations without a full-time in-house IT team
- Companies that want to reduce the workload of the existing IT team
- Businesses seeking external support in specialised areas
- Managers who want to make their costs predictable
In Which Areas Do We Offer Consultancy?
Outsourced IT Support
- User support services (Helpdesk)
- Remote and on-site intervention
- Hardware, software and peripherals support
- Remote and on-site intervention
- Hardware, software and peripherals support
System & Infrastructure Management
- Server and virtualisation management
- Network devices and security infrastructure
- Update, maintenance and monitoring processes
- Network devices and security infrastructure
- Update, maintenance and monitoring processes
Security & Continuity Services
- Endpoint security management
- Backup and disaster recovery
- Authorisation and access controls
- Backup and disaster recovery
- Authorisation and access controls
IT Operations and Reporting
- Periodic status and performance reports
- Risk and improvement suggestions
- Transparency at management level
- Risk and improvement suggestions
- Transparency at management level

Our Working Model
Analysing your current IT processes
Clarification of outsourcing scope
Determination of SLA and responsibilities
Operation takeover
Continuous monitoring, reporting and improvement
FREQUENTLY ASKED QUESTIONS
Clear Answers to Visitor Questions
❓ Why should we outsource when we have our own IT staff?
Outsourced services complement your existing team. It provides continuity, expertise and cost advantages; it eliminates the risks of leave, sickness and staff turnover.
❓ How is the service level guaranteed?
Response times, scope and responsibilities are determined in writing with a clearly defined SLA (Service Level Agreement).
❓ Is there an information security risk?
All access is authorisation based. Privacy, data security and access policies are secured under the contract.
❓ How do we get support in emergencies?
Prioritised intervention processes and fast action plans are in place for critical situations.

SONOTEK INFORMATION TECHNOLOGIES
Why Us?
Corporate discipline and experience in the field
Predictable cost model
End-to-end IT management from a single point
Transparent reporting and clear SLAs
Customised flexible service structure
FIRST STEP
Free Preliminary Evaluation
Let's analyse your IT processes together.
Let us determine the most suitable outsourcing model for you.


