
Acronis Advanced DLP
Acronis DLP is a solution designed specifically for Managed Service Providers (MSPs), preventing sensitive data from leaking over peripheral devices (USB, printer) and network channels. The system is capable of automatic policy creation to eliminate complex configuration processes.
The platform's prominent capabilities are:
- Automatic Policy Creation: “Thanks to the ”Observation mode", it automatically creates business-specific rules by monitoring user behaviour.
- Comprehensive Control: It provides context-aware control over peripheral devices, clipboard, network communications (email, cloud) and even text in graphical formats (with OCR).
- Adaptive Protection: It comes with ready-made data classifiers such as PII, PHI and PCI DSS; it also offers customisable rules based on file type.
- Flexible Management: It offers flexible options such as strict enforcement mode or allowing users to temporarily unblock for business reasons (Block override).
- Visibility and Reporting: It provides full control with real-time alerts, policy-based logging and detailed event viewer.
In short, it is a security solution that minimises the installation and management burden of MSPs with artificial intelligence and automation while preventing data leaks.
Content and context sensitive DLP controls
Prevent sensitive data leakage from customers' organisations. Acronis DLP detects the sender, recipient, channel used and sensitive content in each data transfer to implement policy-based preventive DLP controls.
Content-aware control over data streams to peripheral devices
Control data transfers across customers' organisations to peripheral devices such as printers, removable storage and mapped drives and ensure that no sensitive data in use is leaked through such local channels.
Network communication control
Control data transfers through network channels such as emails, cloud file sharing services, web browsers and social media. Prevent leakage of sensitive data in motion across customers' organisations.
Pre-built data classifiers
Protect customers" sensitive data out of the box with pre-built data classifiers for Personally Identifiable Information (PII), Protected Health Information (PHI), payment card data (PCI DSS) and documents marked "Confidential".
Strict DLP policy enforcement (Enforcement mode)
For customers that require stricter controls, you can apply DLP policies as defined and also block new data flows that are not observed during the observation mode period.
Clipboard control for remote connections
Prevent data leaks at the earliest stage - when data is being transferred between the corporate computer and BYOD devices or remote terminals via a routed clipboard.
Optical character recognition (OCR)
Prevent leakage of textual data in graphic format, even for offline and remote endpoints. Benefit from agent-resident optical character recognition for more than 30 languages without sending images to OCR servers.
Content review and filtering
Prevent leakage of customers' sensitive data by analysing and filtering the textual and binary content of data transmitted through local and network channels, including inspection of nested archives. Leverage text parsing for more than 100 files, 40+ archives, and five print formats.
Real-time warning
Empower policy-based, real-time alerts for relevant DLP events to increase visibility for DLP administrators and enable them to react to critical security events in a timely manner.
Policy-based logging
Enable easy auditing and IT investigations by automatically and selectively collecting audit logs of security events for each DLP policy rule. Benefit from configurable log retention settings as well as cloud-native, secure, always-available centralised log and secure delivery.
DLP event viewer
Increase the efficiency of your service technicians by providing a single-pane-of-glass view of all DLP events with quick search and filtering capabilities.
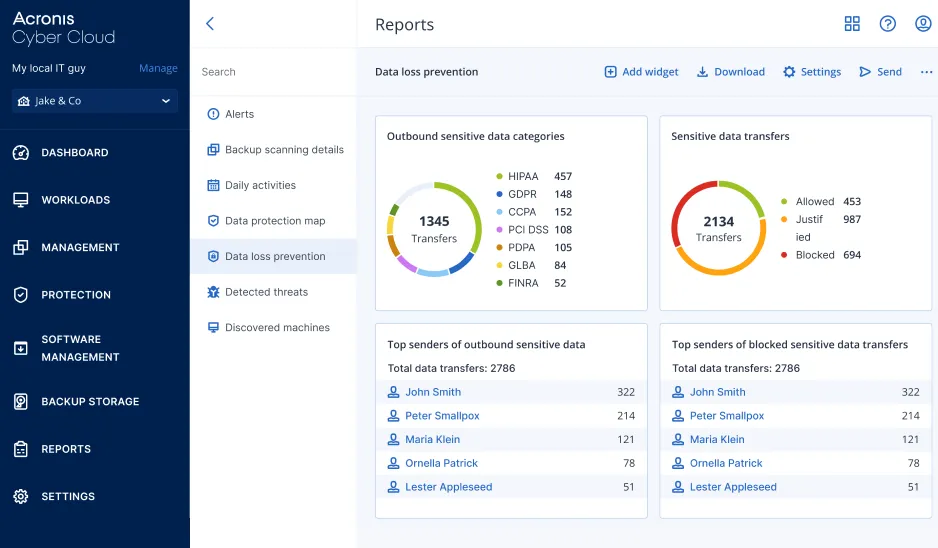
Reporting
Demonstrate your service value to customers and streamline compliance reporting with information-rich tools (widgets) that provide a clear view of actionable data loss prevention statistics that can be easily sent to customers as reports.
On-screen notification to end users
Increase end users' awareness of data loss prevention and reduce the time IT administrators spend investigating with interactive on-screen alerts that explain why specific data transfer attempts are blocked by DLP rules.
Block override support
Ensure customer business continuity by allowing end users to override data transfer blocking by providing a one-time business-related exception in the event of a disaster.
Support for encrypted removable storage
Better protect customer data by neutralising the risks of sensitive data leaving your customers' workloads via unencrypted removable storage devices (e.g. USBs). Acronis DLP can detect encrypted removable storage devices and only allow data transfer to them.
Customise DLP rules based on file type
Gain more granular control over DLP rules and reduce the risk of sensitive data leakage on customer endpoints by customising DLP policy with rules that prevent unauthorised transfer of specific sensitive file types.
Free Preliminary Evaluation
Your system and network infrastructure
Let's design together according to the needs of today and tomorrow.




