Acronis Advanced Security + XDR
- Home Page
- Solutions
- Acronis Security Solutions
- Acronis Advanced Security + XDR
Acronis Advanced Security + XDR
Acronis XDR is a comprehensive solution that combines cyber security, data protection and endpoint management on a single platform, eliminating the complexity and cost of multiple security products. System, Acronis Copilot GenAI assistant enables technical teams to analyse incidents and intervene quickly using natural language.
The platform's prominent capabilities are:
- Integrated Response: Thanks to the integration of cyber security and data protection, it is possible to isolate the endpoint in case of attack, take forensic backup and restore the system with a single click.
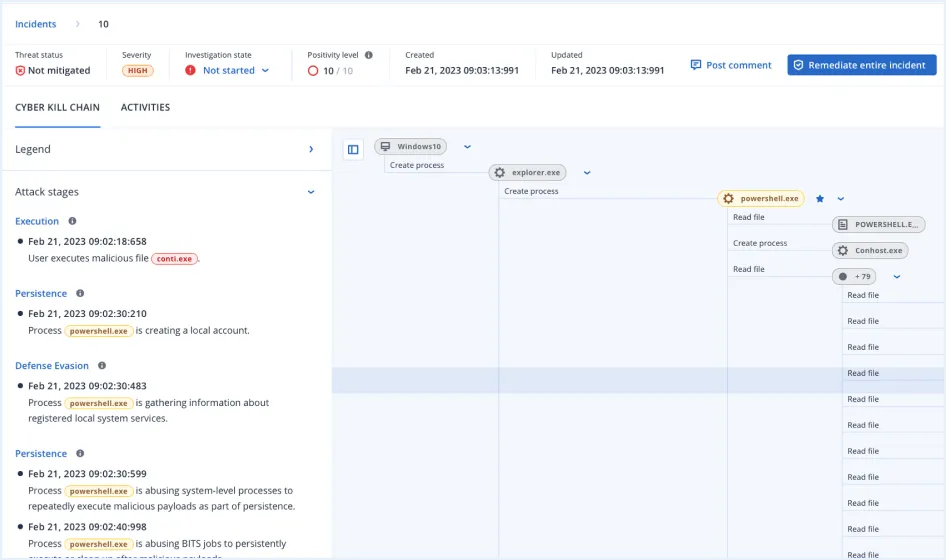
- Automation and Intelligence: Automated incident interpretation, AI-powered incident summaries and automated response scenarios (playbooks) paired with MITRE ATT&CK.
- Comprehensive Integration: Increase threat visibility by integrating with email security, Entra ID, and Microsoft 365 collaboration tools.
- Safe Recovery: Safe Recovery and Attack-specific rollback features to clean backups from malware.
- Proactive Protection: Predetermine risks with real-time threat intelligence, patch management, vulnerability scans and #CyberFit score.
In short, it reduces operational load and maximises security by managing the entire process from incident detection (EDR/XDR) to business continuity (Backup/DR) from a single console.
Acronis Copilot: Your GenAI security assistant
Streamline operations for highly specialised technicians while enabling MSP technicians with limited safety skills to respond effectively and quickly to incidents. Conduct richer investigations, respond faster, and mitigate risks at scale in minutes using only natural language through a conversational user experience with the GenAI assistant. Users can:
- Interacting with Acronis Copilot to ask specific questions about an event.
- To receive advice on actions to mitigate threats.
- To get a list of events with similar detections for deeper analysis.
Automatic response scenarios (Playbooks)
Automate response to XDR and EDR events to scale your security operations and improve response times, while reducing the operational burden of managing security events. Grow your business worry-free, knowing you can protect more businesses and workloads without adding additional resource needs.
Comprehensive response to attacks for unrivalled business continuity
Prevail where point solutions fail - harness the full power of integration between cybersecurity, data protection and endpoint security configuration management with one-click incident response:
- Optimise: By isolating endpoints and quarantining threats.
- Find out more: Using remote connections and forensic backups.
- Prevent future attacks: By closing open vulnerabilities.
- Ensure business continuity: With integrated backup and recovery.
Attack specific rollbacks (Rollbacks)
Quickly and easily undo attack damage, including affected files, data and configurations, making it easy to remediate without relying on the vulnerable Microsoft Volume Shadow Copy Service (VSS) that most solutions use.
Automatic interpretation of events paired with MITRE ATT&CK®
Accelerate response and increase reactivity to threats by leveraging AI-based attack interpretations paired with MITRE ATT&CK® to understand, in minutes How did the attacker get in? How did he cover his tracks? What kind of damage was done? How did the attack spread?
Event summaries generated by artificial intelligence (AI)
Further accelerate incident analysis and response times by leveraging AI-generated summaries that provide a brief overview of each incident.
Prioritisation of events
Focus on what's important and increase your speed of response to attacks with automated event alerts prioritised by criticality, so your team can focus on troubleshooting rather than threat hunting.
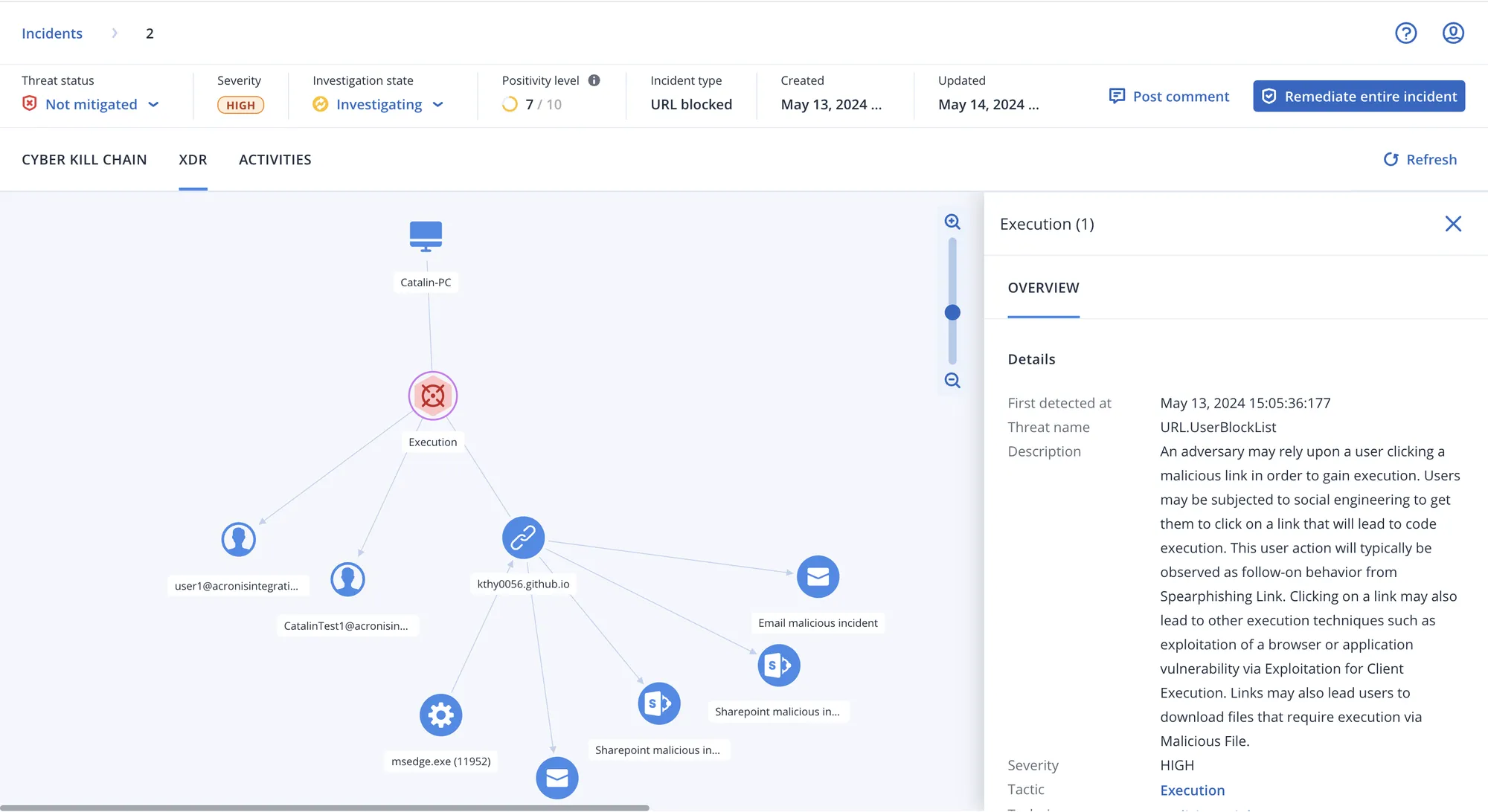
Integration with Email Security (Perception Point)
Gain increased telemetry by integrating rich forensic data from Acronis' best-in-class Email Security solution. Understand if the attack originated from an email and respond by removing malicious attachments and URLs, searching more mailboxes for the threat, or blocking the sender's email address.
Integration with Entra ID
Leverage advanced visibility and response capabilities for attacks that exploit compromised credentials; detect compromised user accounts, terminate their sessions, force password resets, or suspend the account entirely.
Integration with Collaboration Security (for Microsoft 365 applications)
Cloud applications such as Microsoft 365 Teams, SharePoint, and OneDrive are increasingly targeted in attacks. Ensure you can overcome such threats with natively integrated telemetry and response actions for Microsoft 365 applications.
Threat containment and quarantine
Remediate attacks by stopping malicious processes and quarantining analysed threats to prevent them from being executed as part of unified, one-click response capabilities.
End point isolation
Stop attacks from spreading and affecting more endpoints; you can isolate affected points from the network to prevent lateral movement.
Recovery and full image restoration (Reimaging)
Ensure customers' business is always up and running, quickly recovering data and operability after attacks. With best-in-class backup and recovery capabilities integrated into our one-click response system, you can recover specific files or reinstall an image of the entire endpoint.
Disaster recovery failover (with Disaster Recovery)
Provide unparalleled business continuity with integrated disaster recovery. Automatically transition to a backup, off-site environment in the event of attacks that disrupt customer business continuity.
Remote connection to endpoint (with Acronis RMM)
Investigate incidents further with secure remote connectivity to affected endpoints for troubleshooting and additional analysis purposes.
Forensics backup
Gather evidence for further investigation, reporting, compliance and legal purposes by collecting forensic information such as memory dumps and process information and storing it in tamper-proof backups.
Patch management (with Acronis RMM)
As part of a one-click response to attacks, you can close vulnerabilities to prevent recurrence of future incidents with our integrated patch management for more than 250 applications.
Event monitoring and automatic correlations
The solution tracks events at the endpoint level and automatically correlates them in a per-event attack chain graph.
Intelligent search for IoCs focussing on emerging threats
Instead of scanning hundreds of lines of logs, focus on what matters, such as indicators of compromise (IoCs) related to emerging threats from our real-time threat intelligence feeds, and automatically search for IoCs across all endpoints.
Malware protection for backups
Prevent infected files from being restored from backups with built-in malware scanning, including encrypted backups. Acronis Cyber Protect Cloud scans full-disk backups in a central location to help find malware and enable users to restore a clean and malware-free backup.
Safe recovery
Prevent dangerous infections from occurring again with Acronis' unique secure recovery technology. During the recovery process, the integrated solution scans the backup for malware, installs the latest security patches and updates antivirus databases.
Remote device wipe
Prevent business-critical data from falling into the wrong hands by remotely wiping compromised or lost Windows devices. You can prevent data from being wiped by disgruntled employees or accessed from lost/stolen devices.
Real-time flow of threat intelligence
Acronis Cyber Protection Operations Centres (CPOC) constantly monitor the cybersecurity environment and issue alerts about any potential threats. Receive real-time alerts about malware, vulnerabilities, natural disasters and other global events that could affect data protection, so you can prevent them.
Exploit prevention
Prevent advanced attack techniques, including zero-day and fileless attacks, with behaviour-based detection heuristics focused on vulnerability exploitation. Acronis' exploit prevention technology specifically detects attempts to exploit software vulnerabilities.
Ransomware detection with automatic rollback
Detect and stop ransomware, including advanced complex forms, and automatically roll back changes caused by the threat or data affected.
Behaviour-based detection
Protect customers, their data and operations against modern threats with award-winning protection to detect typical patterns of malicious behaviour and prevent threats from operating.
URL filtering
Help your customers achieve compliance and increase productivity by preventing attacks from malicious websites. Acronis URL filtering allows you to control website access via an HTTP/HTTPS blocker, manage exceptions for URLs and perform payload analysis.
Unprotected endpoint discovery
Ensure there are no gaps in customer defence by facilitating discovery of unprotected endpoints and enabling remote agent deployment and service provisioning.
Vulnerability assessments
Monitor endpoints for open vulnerabilities and streamline attack detection and response as well as security configuration management by providing a prioritised view based on vulnerability criticality.
#CyberFit Score to assess the security posture of endpoints
Quickly and easily assess the security posture of endpoints and utilise our guided recommendations to secure customer endpoints. Unlock a unified view of all endpoints as well as #CyberFit Scores to simplify security configuration management.
Data classification (with DLP)
When investigating attacks, increase your visibility over affected data by classifying outbound data from customer endpoints to detect and stop sensitive data leakage with greater efficiency.
File and system level backup
Ensure that not only endpoints are protected, but also the data on them. Take advantage of pre-integrated, best-in-class backup capabilities that provide unparalleled data protection and business continuity.
Device and port control
Strengthen data security and prevent sensitive information from leaking over local channels with controls over user access to (and data transactions on) locally connected devices and ports - even for virtualised sessions.
Automatic, adjustable allowlisting based on profiling
To save time and prevent resource-consuming false positives, you can enable monitoring and profiling of customer applications to create an automatic allowed list of the most used applications, including custom applications. You can also manually add or remove apps from the list.
Enhancing Microsoft Defender AV
Acronis EDR enhances Microsoft Defender with advanced, AI-powered analysis, detection, response and recovery. MSPs gain centralised visibility, enhanced protection and built-in resiliency without replacing Defender to scale profitably.
Potentially unwanted application (PUA) protection
Protect against potentially unwanted applications (PUAs) that can degrade system performance, display annoying adverts or monitor user activity for commercial purposes. When detected, PUAs are quarantined or blocked according to policy settings and relevant details are integrated into EDR events for further analysis.
| Features | Acronis Cyber Protect Cloud | EDR | XDR |
| Behaviour-based detection | ✔ | ✔ | ✔ |
| Ransomware protection with automatic rollback | ✔ | ✔ | ✔ |
| Vulnerability assessments | ✔ | ✔ | ✔ |
| Device control | ✔ | ✔ | ✔ |
| File and system level backup | ✔ | ✔ | ✔ |
| Inventory collection (with Acronis RMM) | ✔ | ✔ | ✔ |
| Patch management (with Acronis RMM) | ✔ | ✔ | ✔ |
| #CyberFit Score (security posture assessment) | ✔ | ✔ | ✔ |
| Remote connection (with Acronis RMM) | ✔ | ✔ | ✔ |
| Optimisation including full image refresh | ✔ | ✔ | ✔ |
| Business continuity (with Disaster Recovery) | ✔ | ✔ | ✔ |
| Enhancing Microsoft Defender AV | ✔ | ✔ | ✔ |
| URL filtering | ✔ | ✔ | ✔ |
| Exploit prevention | ✔ | ✔ | ✔ |
| Real-time flow of threat intelligence | ✔ | ✔ | ✔ |
Threat hunting - Early access | ✔ | ✔ | |
Automatic, adjustable allowed list based on profiling | ✔ | ✔ | |
Forensic data collection | ✔ | ✔ | |
| Event monitoring | ✔ | ✔ | |
Automatic event correlation | ✔ | ✔ | |
GenAI assistant (Acronis Copilot - Early Access) | ✔ | ✔ | |
Prioritisation of suspicious activities | ✔ | ✔ | |
AI-generated event summaries | ✔ | ✔ | |
Automated MITRE ATT&CK® attack chain visualisation and interpretation | ✔ | ✔ | |
One-click response to incidents | ✔ | ✔ | |
Full threat containment including endpoint quarantine and isolation | ✔ | ✔ | |
Automatic response scenarios (playbooks) | ✔ | ||
Intelligent search for IoCs, including emerging threats | ✔ | ||
Attack-specific undo | ✔ | ||
Integration with Email Security (email telemetry) | ✔ | ||
Integration with Entra ID (identity telemetry) | ✔ | ||
Integration with Collaboration Security (telemetry of Microsoft 365 applications) | ✔ | ||
Delete malicious email attachment or URLs | ✔ | ||
Search for malicious attachments in mailboxes | ✔ | ||
Blocking malicious email address | ✔ | ||
Terminate all user sessions | ✔ | ||
Force user account password reset on next login | ✔ | ||
User account suspension | ✔ | ||
| MDR service | ✔ | ||
General API for EDR | ✔ |
Free Preliminary Evaluation
Your system and network infrastructure
Let's design together according to the needs of today and tomorrow.



